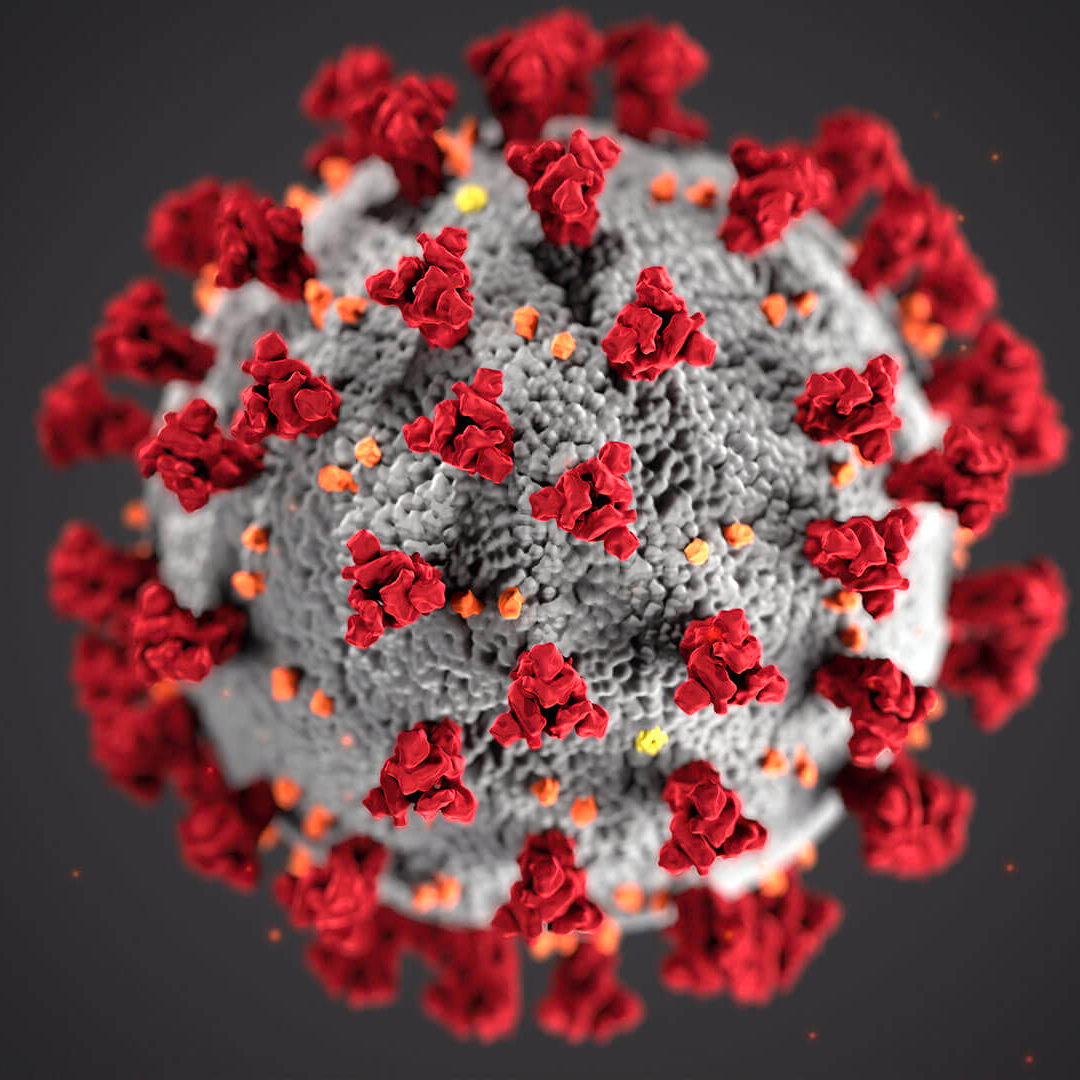
Best Practices: WFH Security
For over a decade prior to Coronavirus/Covid-19, Victory has been enabling remote teams for SMB and Enterprise companies. Based on our experience here are some best practices that have historically lent themselves to a successful evolution to an all remote workforce, or Work From Home (WFH) team.
It’s not an emergency until it IS…
The United States took COVID-19 seriously on a Friday – and even then most people thought they would go to work as usual on Monday. Many businesses did not plan for their team to be entirely remote but here we are. Later we will showcase a Victory client that made the switch from fully on site to fully remote as the crisis was hitting home.
What’s next?
The office is a walled garden – IT controls what comes in and out at the perimeter and keeps things reasonably safe. Outside of those walls, however, it becomes more challenging. Your team members’ homes are not necessarily any more secure than a public hotspot. The following two technologies allow teams to securely connect to business networks from home, the right solution depends on they size and nature of your business.
Virtual Private Networks (VPN)
A Non-Technical Definition of VPN:
VPNs create a secure connection to external networks, like to the one at your office, across the internet. Connecting to the internet on public wifi (think coffee shop) without a VPN, means that when your computer sends and receives messages they are unencrypted and could be intercepted, which is a security risk.
There are a lot of public VPN services out there which will protect you when on public or untrusted networks; here is a list. Configuration for your specific security needs is critical. As a baseline, make sure that your VPN includes local network isolation (often called local firewall) so that your computer is fully isolated from the local network.
Everyone should have a VPN on every device - period.
-Every IT Professional Ever
But that’s not the point of this article – this is about allowing your people to work on corporate systems securely. Many companies rely on whitelisted IP addresses or local networks, especially to secure legacy systems. To allow your people to log in you need a corporate VPN – which can be very expensive and complex. Our team can help you navigate OpenVPN, Algo and other solutions that not only meet your needs but also your budget. We implement solutions in a short time on commodity hardware and allow your employees to log in to the office network and be in the office virtually.
Secure Remote Desktops (SRD)
First, as a light case study: Victory was recently called on to mobilize a 50+ team member Suddenly Remote Workforce mentioned at the beginning of this article. For security’s sake to date, everyone was required to work on premises because the company handles sensitive financial data. However, due to coronavirus, the state mandated they close the office immediately, leaving the company stranded without any course of action to restore productivity.
Victory was engaged to implement an already-in-a-disaster recovery & backup plan, and as always, time was literally money. Victory accomplished this by creating a Secure Virtual Office using Amazon Web Services (AWS) Workspaces. In a controlled rollout on Monday, 10% of the workforce logged into Secure Remote Desktops from home. On Tuesday, the office was closed and the remainder of the employees migrated to SRDs from home. With seamless continuity, the business didn’t skip a beat.
Secure Remote Desktops (SRD) are one of the most secure ways to address security concerns for a remote team.
There are some distinct advantages to SRDs:
- SRDs can be managed by the same Directory service as the main office – user roles, permissions and even drive contents will transfer seamlessly
- Connection to the SRD is a secure encrypted tunnel
- Files on the SRD cannot be downloaded to the user’s device
- You can connect from a Windows or Mac Laptop, iPad, iPhone, Android Phone or Tablet
- The desktop itself is connected to one of the fastest and most durable connections possible
Note: SRDs dovetail with Victory’s Azure Active Directory offering. If you have Active Directory on premise we can migrate to the Cloud and add SRDs at the same time, and they are available in AWS or Azure cloud. With Azure AD security can be implemented down to the document.